Set up CyberArk Conjur for workspace-level secrets management
Existing external secrets references that are scoped to the project level will stop working when you switch to workspace-specific secrets management.
FEATURE AVAILABILITY
Secrets management is available to customers on specific pricing plans. Refer to your pricing plan and contract to learn more.
Conjur host configuration for Workato
Integration between Workato and Conjur is based on the host/workload API key authentication.
For Workato to retrieve a secret from your Conjur instance, an API authentication request is first sent to your Conjur server based on the parameters specified when configuring the CyberArk Conjur connector. If the credentials are valid, Conjur responds with a short-lived access token. Workato then uses this access token to retrieve the actual secret value stored in Conjur if the host has the necessary execute and read permissions.
Policies on Conjur are written as .yml files. Visit the CyberArk Conjur documentation for policy best practices. The following steps describe how to develop a policy file.
For more information on policy syntax operators, refer to the CyberArk Conjur documentation.
Declare a group at the root policy:
- !policy
id: workato-app
body:
- !group workato-secret-usersDeclare variables and assign the group [read, execute] permissions.
This example creates the sql-password-prod and sql-host-prod variables which store the password for a SQL database as well as the host name:
- &variables
- !variable
id: sql-password-prod
kind: password
- !variable
id: sql-host-prod
kind: password
- !permit
role: !group /workato-app/workato-secret-users # group declared earlier
privileges: [read, execute]
resources: *variablesDeclare the host, a layer, and assign membership of the host into the layer:
- !host workato-us-prod-1
- !layer workato-us-prod
- !grant
role: !layer workato-us-prod
members:
- !host workato-us-prod-1Grant membership of the layer into the group:
- !grant
role: !group workato-app/workato-secret-users
member: !layer workato-app/ workato-us-prodGrant execute and read permissions to group on selected variables:
- !permit
role: !group /workato-app/workato-secret-users # layer declared earlier
privileges: [read, execute]
resources: !variable ddog-api-keyExpand for an example of a full policy
- !policy
id: workato-app-dev
body:
- !group workato-secrets-dev
- &variables
- !variable
id: sql-password-prod
kind: password
- !variable
id: sql-host-prod
kind: password
- !permit
role: !group /workato-app-dev/workato-secrets-dev # group declared earlier
privileges: [read, execute]
resources: *variables
- !host workato-us-dev-1
- !layer workato-us-dev
- !grant
role: !layer workato-us-dev
members:
- !host workato-us-dev-1
- !grant
role: !group workato-secrets-dev
member: !layer workato-us-devTo which the expected response would be:
{
"created_roles": {
"workato:host:workato-app-dev/workato-us-dev-1": {
"id": "workato:host:workato-app-dev/workato-us-dev-1",
"api_key": "1q3ye3gxxxx"
}
},
"version": 1
}Select the scope and set up CyberArk secrets management
Sign in to your Workato workspace.
Navigate to Workspace admin > Settings > Security > External secrets manager.
In Scope, select the option Set up secrets management for the entire workspace:
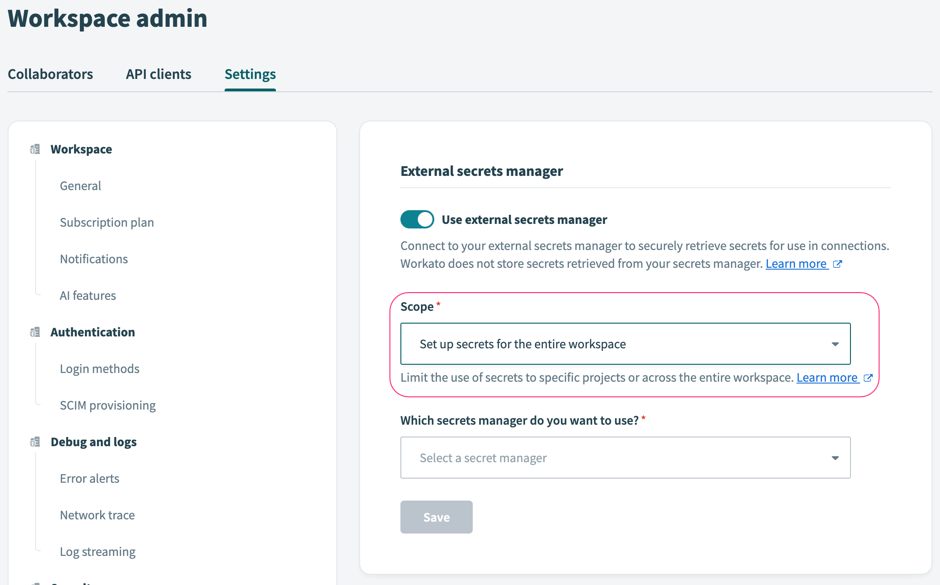 Set up secrets management for the entire workspace
Set up secrets management for the entire workspace
In the Which secrets manager do you want to use? field, select CyberArk Conjur:
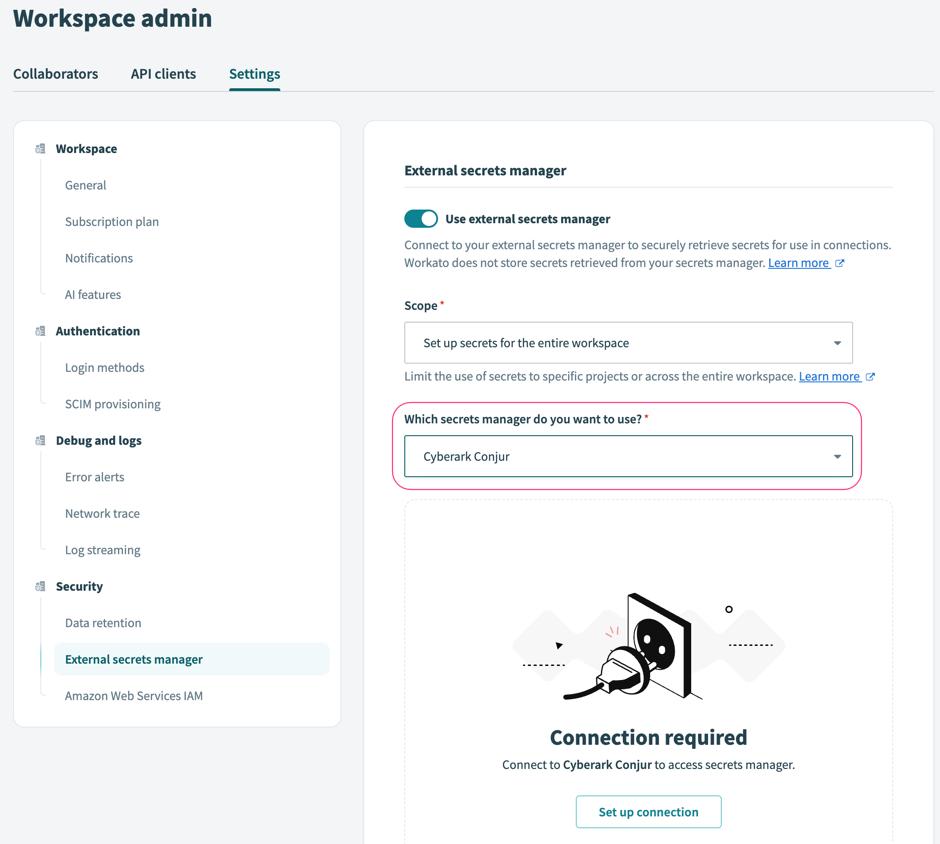 Secrets management interface of a workspace
Secrets management interface of a workspace
Click Set up connection.
Configure the following fields in Workato:
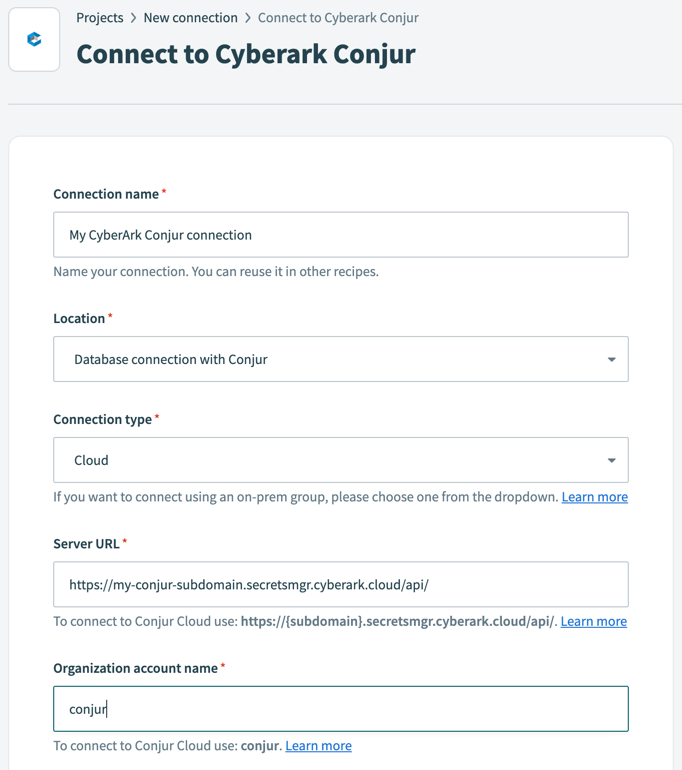 Configure CyberArk Conjur connection
Configure CyberArk Conjur connection
Connection name
Name your CyberArk Conjur connection.
Connection type
Workato supports both cloud and on-prem connection types. If you plan to use an on-prem group, select one from the drop-down.
Server URL
To connect to Conjur Cloud, the server URL must follow this format:
htmlhttps://<subdomain>.secretsmgr.cyberark.cloud/api/Organization account name
To connect to Conjur Cloud, input
conjur.Login ID
For host authentication, the ID must be prefixed with
host/, for example:host/workato-app/workato-user-1.API key
Conjur generates an API key for every user when the user resource is created. Learn more about generating an API key in CyberArk Conjur's documentation.
How to revoke access to secrets store on CyberArk Conjur
To revoke Workato's access to secrets stored on CyberArk Conjur, rotate the host's API key with a PUT request and ensure that the host ID is URL-encoded:
PUT {{conjurServer}}/authn/{{conjurOrganization}}/api_key?role=host:workato-conjur-demo/workato-us-2Secrets are no longer accessible after sixty minutes.
To revoke access immediately, rotate the API key, then use the clear_cache API.
For more information, consult the Conjur documentation on how to rotate host API keys.
This process applies to both CyberArk Conjur Enterprise and CyberArk Conjur Open Source. Visit the Cyberark Conjur Cloud-specific documentation for more information.
Last updated: