# Microsoft Entra ID SAML configuration
This guide describes how to configure Microsoft Entra ID as a SAML identity provider (IdP) for Workato Identity.
SAML enables secure authentication between an IdP, such as Microsoft Entra ID, and a service provider like Workato. Users authenticate once through Microsoft Entra ID and gain access to Workato with a single login instead of managing separate credentials for each application. Refer to Microsoft Entra ID SAML-based authentication (opens new window) documentation for more information.
PREREQUISITES
Workato Identity is available for Agent Studio, Workato GO, MCP, and the API developer portal.
Configure SAML-based authentication in Workato Identity before you begin. The Specify Single sign-on URL and Service provider (SP) entity ID values from that setup are required to complete the following steps.
# Configure SAML authentication in Microsoft Entra ID
Complete the following steps to configure SAML authentication in Microsoft Entra ID:
NOT FOR WORKFLOW APPS SAML-BASED SSO
This documentation is specific to Workato Identity. Refer to SAML-based single sign-on authentication to configure SAML authentication for Workflow apps.
Sign in to the Microsoft Entra admin center (opens new window) or the Azure portal (opens new window).
Go to Identity > Applications > Enterprise applications and click New application.
Click Create your own application.
Enter a name for the app in the What's the name of your app? field. For example, Workato Agentic or MCP Servers.
Select Integrate any other application you don't find in the gallery (Non-gallery) and click Create.
Go to Manage > Single sign-on and select SAML as the single sign-on method.
Go to the Basic SAML Configuration section and click Edit.
Paste the Service provider (SP) entity ID from Workato into the Identifier (Entity ID) field.
Paste the Single sign-on URL from Workato into the Reply URL (Assertion Consumer Service URL) field.
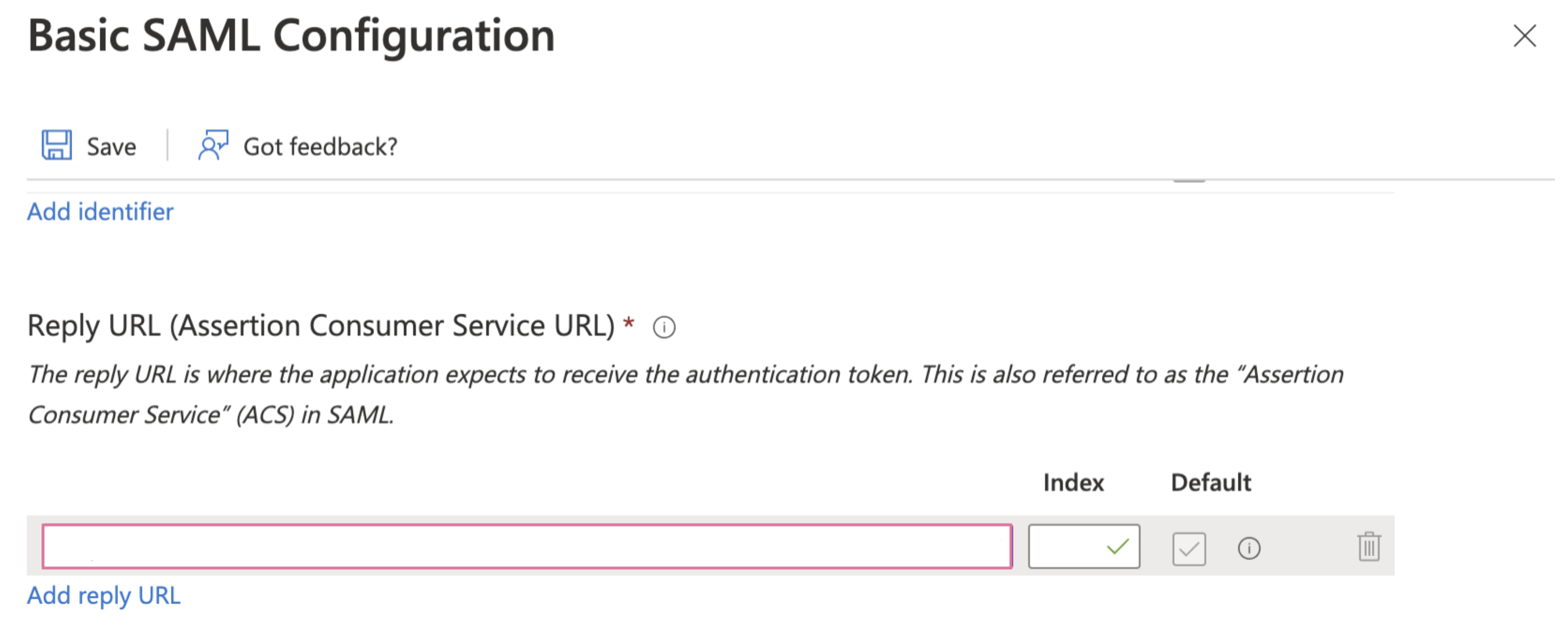 Paste the Single sign-on URL from Workato into the Reply URL (Assertion Consumer Service URL) field
Paste the Single sign-on URL from Workato into the Reply URL (Assertion Consumer Service URL) field
Click Save.
Go to the Attributes & Claims section and click Edit.
Click + Add new claim and add the following attribute:
| Name | Source attribute |
|---|---|
workato_end_user_name | user.displayname |
Click Save.
Click + Add a group claim and configure the following settings:
| Setting | Value |
|---|---|
| Which groups should be returned in the claim? | Groups assigned to the application |
| Source attribute | Cloud-only group display names |
| Customize the name of the group claim | Enabled |
| Name | workato_end_user_groups |
| Namespace | Leave empty |
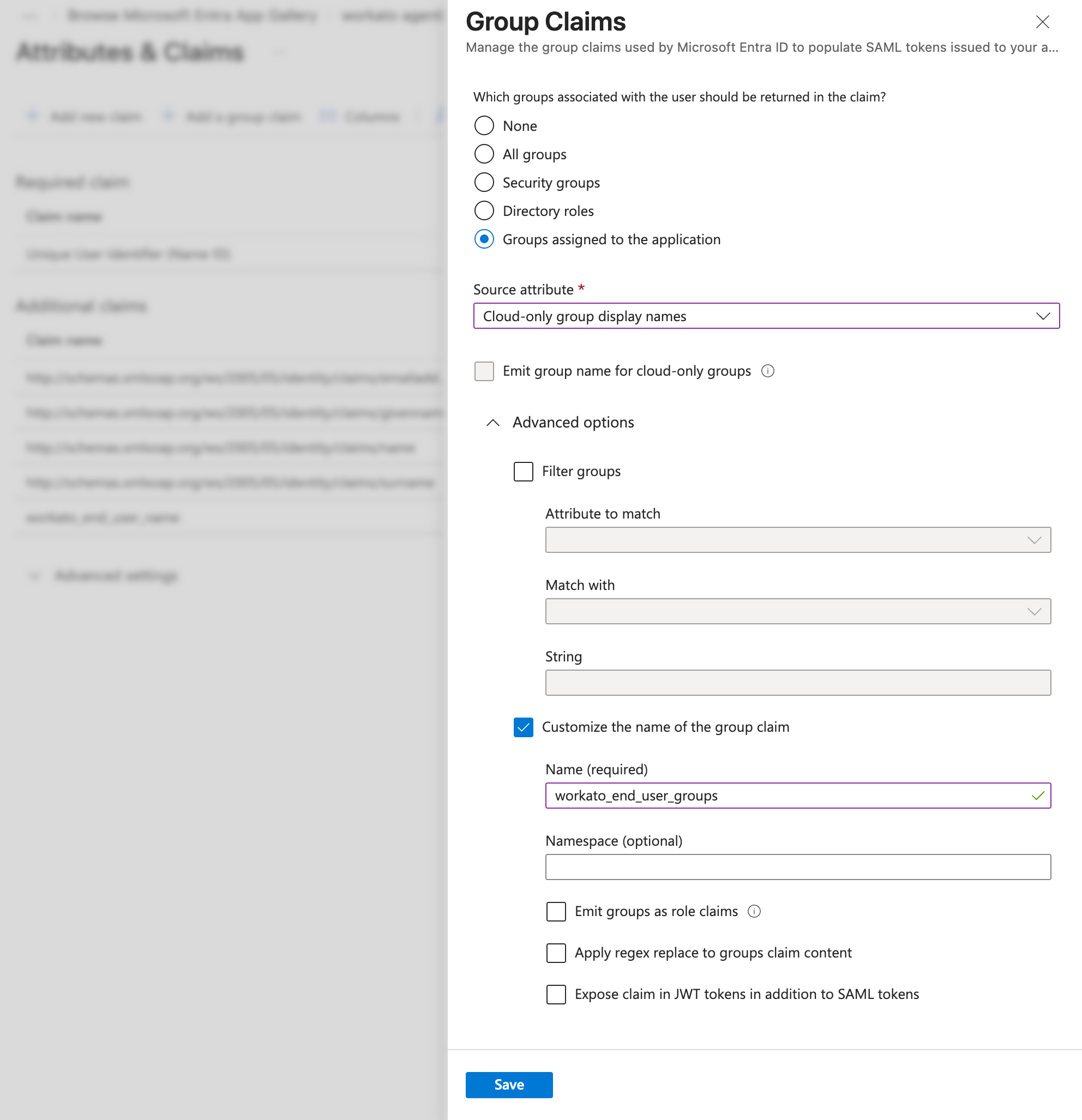 Configure the group claims settings in Microsoft Entra ID
Configure the group claims settings in Microsoft Entra ID
Click Save.
Go to Manage and select Users and groups.
Click Add user/group and add one or more users or groups that should have access to the application.
Click Assign.
Return to Single sign-on and scroll to the SAML Certificates section.
Copy the App Federation Metadata URL. You must use this URL in the Do you have your identity provider metadata URL? section of the Set up a new provider modal in Workato Identity.
Return to your Microsoft Entra ID account and go to Properties.
Set Visible to users? to No to prevent the app from appearing in the user's app launcher.
DIRECT SIGN-IN FROM IDP UNSUPPORTED
You can't sign in to Workato directly from your IdP. Authentication is only supported when initiated through a conversation in your connected LLM.
Last updated: 4/14/2026, 3:25:07 PM